By: Augusto Remillano II and Jakub Urbanec
We discovered a new variant of Mirai (detected as Backdoor.Linux.MIRAI.VWIPT) that uses a total of 13 different exploits, almost all of which have been used in previous Mirai-related attacks. Typical of Mirai variants, it has backdoor and distributed denial-of-service (DDoS) capabilities. However, this case stands out as the first to have used all 13 exploits together in a single campaign.
This attack comes just a few weeks after we last reported on Mirai activity, when it had targeted various routers. Several exploits used in the previous attack have also been used by this variant.
The new Mirai variant
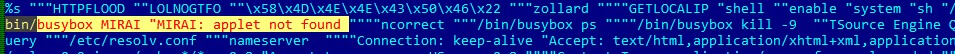
Our initial findings on the new variant came from one of our honeypots dedicated to looking for attacks related to the internet of things (IoT). It showed that this malware used different means of spreading, and also revealed its use of three XOR keys to encrypt data. Decrypting the malware’s strings using XOR revealed one of the first relevant indicators of the malware’s being a Mirai variant. The decrypted string can be seen in Figure 1.
- 0x22 (standard Mirai strings)
- 0x37 (strings with “watchdog”)
- 0xea (credentials for brute force attack: “telecomadmin”, “admintelecom”, etc.)
Figure 1. Decrypted string showing Mirai connection
We also found the different URLs used by this variant. The first URL on the list below worked as the command-and-control (C&C) link, while the rest served as download and dropper links. In the download and dropper links, of note is the use of hopTo, a free dynamic DNS (Domain Name Server) provider.
- hxxp://32[.]235[.]102[.]123:1337
- hxxp://ililililililililil[.]hopto[.]org/shiina/tmp.arm7
- hxxp://ililililililililil[.]hopto[.]org/shiina/tmp.mips
- hxxp://ililililililililil[.]hopto[.]org/love.sh
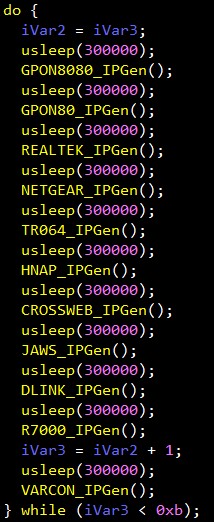
Looking into the new variant’s code revealed more details about how it spreads, specifically the 13 different exploits it uses. The first three exploits, shown in Figure 2, are the scanners for specific vulnerabilities found in the web development format ThinkPHP and certain Huawei and Linksys routers. The scanners for the remaining 10 vulnerabilities used in this attack, shown in Figure 3, can be found inside exploit_worker().
We found that aside from spreading through these vulnerabilities, this Mirai variant also has brute-force capabilities using several common credentials listed in the Indicators of Compromise (IoCs) section below.
The exploits
As previously mentioned, this variant is the first Mirai variant to have used all 13 exploits in a single campaign. These exploits take advantage of flaws found in routers, surveillance products, and other devices. However, this is not the first time we’re seeing the 13 used by cybercriminals. All 13 exploits are listed in Table 1 along with other attacks these exploits have been used in.
| Exploit | Vulnerability and affected devices | Relevant attacks | |
| 1 | Vacron NVR CVE | A remote code execution (RCE) vulnerability for Vacron network video recorder (NVR) devices | Omni |
| 2 | CVE-2018-10561, CVE-2018-10562 | Authentication bypass and command injection vulnerabilities, respectively, for the Dasan gigabit passive optical network (GPON) routers | Omni Mirai-like scanning |
| 3 | CVE-2015-2051 | Home Network Administration Protocol (HNAP) SOAPAction-header command execution vulnerability that works on certain D-Link devices | Omni Hakai |
| 4 | CCTV-DVR RCE | RCE vulnerabilities for multiple CCTV-DVR vendors | Omni Yowai |
| 5 | CVE-2014-8361 | Universal Plug and Play (UPnP) Simple Object Access Protocol (SOAP) command execution vulnerability affecting different devices using Realtek software development kit (SDK) with the miniigd daemon | Omni |
| 6 | UPnP SOAP TelnetD command execution | UPnP SOAP command execution exploiting vulnerabilities in D-Link devices | Omni |
| 7 | Eir WAN side remote command injection | Wide area network (WAN) side remote command injection for Eir D1000 wireless routers | Omni |
| 8 | Netgear Setup.cgi RCE | RCE targeting Netgear DGN1000 devices | Omni |
| 9 | CVE-2016-6277 | Vulnerability that can allow the execution of remote arbitrary commands in Netgear R7000 and R6400 devices | Omni VPNFilter infection |
| 10 | MVPower DVR shell command execution | Unauthenticated RCE vulnerability in MVPower digital video recorders (DVRs) | Omni |
| 11 | CVE-2017-17215 | Arbitrary command execution vulnerability in Huawei HG532 routers | Omni Satori Miori |
| 12 | Linksys RCE | RCE vulnerability in Linksys E-series routers | TheMoon |
| 13 | ThinkPHP 5.0.23/5.1.31 RCE | RCE for open-source web development framework ThinkPHP 5.0.23/5.1.31 | Hakai Yowai |
Table 1. List of used exploits and other relevant attacks
Of these exploits, 11 had already been used together in 2018 by the Mirai variant Omni, according to a report by Unit 42. The only two exploits that were not part of that previous Mirai campaign but were used by this new variant were the Linksys and ThinkPHP RCEs. These two exploits, however, were used in a more recent attack, which also included four others on the list: the CVE-2018-10561, CVE-2014-8361, UPnP SOAP TelnetD command execution, and CVE-2017-17215 exploits.
We also reported on the use of the CVE-2015-2051 and CCTV-DVR RCE exploits by the Gafgyt variant Hakai and the Mirai variant Yowai, respectively, and detailed how both malware variants also used the ThinkPHP RCE exploit.
Conclusion and security recommendations
The attacker behind this new variant could have simply copied the code from other attacks, and with it the exploits these previous cases had used. Also, the choice of exploits used by the attacker could’ve been based on the knowledge that many of the affected devices are widely used, and that many users have yet to implement the released patches for the exploited vulnerabilities.
We can only speculate about the motivation behind a campaign.
However, users can already take preventive measures against the spread and success of Mirai variants. These steps include implementing the right patches and updates that will defend against the exploits used by such malware. Users should also take special care in choosing which products to connect to their networks, and consider manufacturers’ security stances and consistency in releasing updates.
Trend Micro solutions
Trend Micro Smart Home Network provides an embedded network security solution that protects all devices connected to a home network against cyberattacks. Based on Trend Micro’s rich threat research experience and industry-leading deep packet inspection (DPI) technology, Trend Micro Smart Home Network offers intelligent quality of service (iQoS), parental controls, network security, and more.
Trend Micro Smart Home Network protects customers from the aforementioned exploits through these rules:
- 1057889: WEB D-Link Devices UPnP SOAP Command Execution (BID-61005)
- 1058632: EXPLOIT Linksys E-series Unauthenticated Remote Code Execution Exploit (EDB-31683)
- 1059669: WEB D-Link Multiple Routers HNAP Protocol Security Bypass Vulnerability (BID-37690)
- 1133255: WEB Remote Command Execution in XML -1
- 1133310: WEB Netgear R7000 Command Injection -1.1 (CVE-2016-6277)
- 1133419: WEB Netgear R7000 Command Injection -1.2 (CVE-2016-6277)”
- 1133498: WEB Remote Command Execution via Shell Script -1.u
- 1133650: WEB Multiple CCTV-DVR Vendors Remote Code Execution
- 1134286: WEB Realtek SDK Miniigd UPnP SOAP Command Execution (CVE-2014-8361)
- 1134287: WEB Huawei Home Gateway SOAP Command Execution (CVE-2017-17215)
- 1134610: WEB Dasan GPON Routers Command Injection -1.1 (CVE-2018-10561)
- 1134611: WEB Dasan GPON Routers Command Injection -1.2 (CVE-2018-10561)
- 1134687: WEB Netgear DGN1000 And Netgear DGN2200 Unauthenticated Command Execution
- 1134812: WEB GPON Routers Command Injection (CVE-2018-10562)
- 1134891: WEB Dasan GPON Routers Command Injection -1.3 (CVE-2018-10561)
- 1134892: WEB Dasan GPON Routers Command Injection -1.4 (CVE-2018-10561)
- 1135215: WEB ThinkPHP Remote Code Execution
- 1135617: WEB VACRON NVR board.cgi cmd Remote Command Execution
Trend Micro Deep Discovery
Deep Discovery provides detection, in-depth analysis, and proactive response to attacks using exploits and other similar threats through specialized engines, custom sandboxing, and seamless correlation across the entire attack life cycle, allowing it to detect these kinds of attacks even without any engine or pattern update. These solutions are powered by XGen
provides detection, in-depth analysis, and proactive response to attacks using exploits and other similar threats through specialized engines, custom sandboxing, and seamless correlation across the entire attack life cycle, allowing it to detect these kinds of attacks even without any engine or pattern update. These solutions are powered by XGen security, which provides a cross-generational blend of threat defense techniques against a full range of threats for data centers, cloud environments, networks, and endpoints. Smart, optimized, and connected, XGen powers Trend Micro’s suite of security solutions: Hybrid Cloud Security, User Protection, and Network Defense.
security, which provides a cross-generational blend of threat defense techniques against a full range of threats for data centers, cloud environments, networks, and endpoints. Smart, optimized, and connected, XGen powers Trend Micro’s suite of security solutions: Hybrid Cloud Security, User Protection, and Network Defense.
Trend Micro  Deep Discovery
Deep Discovery  Inspector protects customers from the mentioned exploits through these rules:
Inspector protects customers from the mentioned exploits through these rules:
- 2385: SOAP RCE EXPLOIT – HTTP (Request)
- 2485: CCTV-DVR Remote Code Execution – HTTP (Request)
- 2543: VACRON Remote Code Execution Exploit – HTTP (Request)
- 2547: NETGEAR DGN1000/DGN2200 Remote Code Execution – HTTP (Request)
- 2548: LINKSYS Remote Code Execution – HTTP (Request)
- 2575: Command Injection via UPnP SOAP Interface – HTTP (Request)
- 2630: HNAP1 Remote Code Execution Exploit – HTTP (Request)
- 2639: CVE-2018-10562 – GPON Remote Code Execution – HTTP (Request)
- 2786: ThinkPHP 5x Remote Code Execution – HTTP (Request)
Indicators of Compromise (IoCs)
Related SHA-256 hash detected as Backdoor.Linux.MIRAI.VWIPT:
- c15382bc81e1bff4cf03d769275b7c4d2d586a21e81ad4138464d808e3bb464c
Related malicious URLs:
| URL | Description |
| hxxp://32[.]235[.]102[.]123:1337 | C&C |
| hxxp://ililililililililil[.]hopto[.]org/shiina/tmp.arm7 | Download link and droppers |
| hxxp://ililililililililil[.]hopto[.]org/shiina/tmp.mips | |
| hxxp://ililililililililil[.]hopto[.]org/love.sh |
Used credentials:
- 12345
- 666666
- 888888
- 20080826
- /ADMIN/
- 1q2w3e4r5
- 3ep5w2u
- admintelecom
- anko
- cisco
- default
- e8ehome
- e8telnet
- guest
- hi3518
- hi3518
- hunt5759
- IPCam@sw
- ipcam_rt5350
- juantech
- juantech
- jvbzd
- jvbzd
- klv123
- klv1234
- klv1234
- password
- qwerty
- QwestM0dem
- service
- service
- smcadmin
- supervisor
- support
- svgodie
- system
- telecomadmin
- ubnt
- xc3511
- xmhdipc
- xmhdpic
- zsun1188
- Zte521
The post New Mirai Variant Uses Multiple Exploits to Target Routers and Other Devices appeared first on .